F06a
| Enigma ID | F06a |
| Name | |
| Frequencies | |
| Status | Active |
| Voice | N/A |
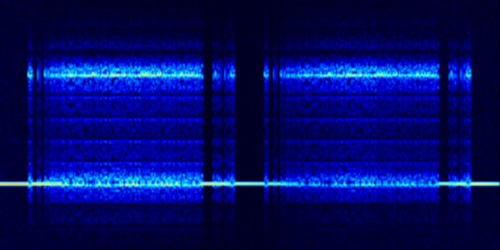
| Emission mode | FSK, 200 Bd, 1000 Hz, ACF=288 |
| Location |
Moscow, Russia; Orenburg, Russia; Chita, Russia
|
| Activity pages |
F06a is a variant of the Russian 6 mode F06. Unlike regular F06, which carries a compressed stream of 5-digit groups, F06a carries a named file.
The regular schedules of F06a consist of 3 identical transmissions 15 minutes apart (as opposed to 10 minutes for regular F06) and transmit unidentified binary files. The transmissions are always repeated the following day, at the same times and frequencies.
File types
The following file types are known to be transported using F06a. Examples of each type may be found in the logs.
| Type | Filename |
|---|---|
| Unidentified binary | "044" or "444" + 2-digit serial number |
| ASCII-encoded text, 5-letter-group telegram |
5-digit link ID + "-~1.TXT" |
| ASCII-encoded text, 5-digit-group telegram |
|
On some schedules or transmissions, binary files start with a short ASCII text header: most often it is the discreet 0x0d0a0d0a0d0a binary sequence which simply corresponds to three empty lines, but occasionally a classic 5-group header appears on the second line. This line spacing is the same as used for 5-group headers at the top of 5-digit/letter-group text telegrams.
Technical details
Each F06a message is structured as follows:
| Byte offset | Length (bytes) | Description |
|---|---|---|
| 0 | 4 | Length of the file contents in bytes, big endian order |
| 4 | 8 | ASCII-encoded file name, padded with 0x00 (NUL) bytes from the left |
| 12 | 4 | ASCII-encoded file extension, including the leading dot; set to 00 00 00 00 if there is no extension |
| 16 | 4 | CRC-32 of the file contents |
| 20 | Variable | File contents |
| 20+N | 1 | A single 0x00 (NUL) byte |
| 20+N+1 | Variable | A string of 0x99 bytes, until the message length is a multiply of 16 bytes |